We Offer

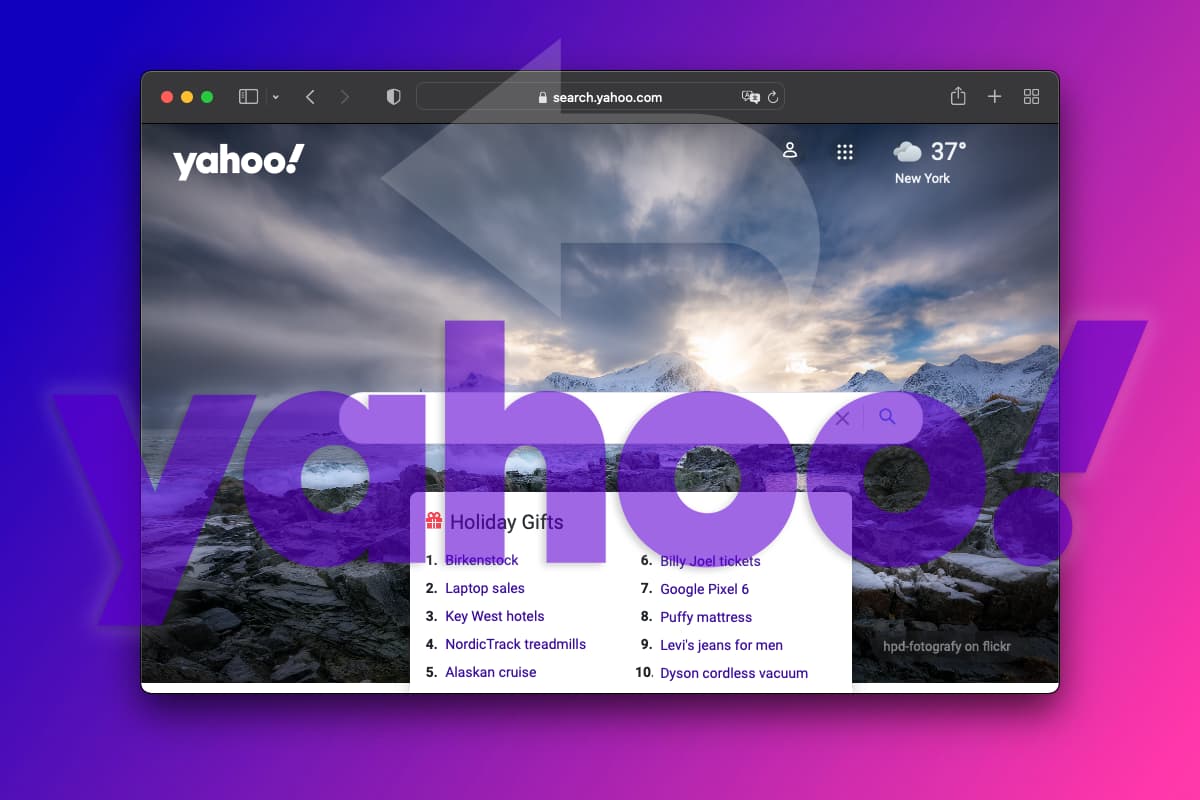
Navigating the maze of Yahoo Search redirect
The smoothness of our online journey is frequently disrupted by

Unleashing Projection Potential: A Guide to Developing Projector Software
Projector software refers to a suite of applications designed to

Bringing Future Film Technologies to the Present: The Intersection of Fiction and Reality
1. Virtual Reality (VR) and Augmented Reality (AR) Virtual reality

A Comprehensive Guide to the Android Operating System
With the increasing popularity of smartphones and tablets, it’s no

Optimizing Your Dissertation: The Fusion of Dissertation Help and Android Operating System
Optimizing your dissertation is key to producing a successful piece

The Power of Android: Unlock the power of your gadget
Android is a popular operating system that powers millions of

Evolution of IoT software development services
As the world of technology advances, we see a dramatic

Development of layouts and functional prototypes of user interfaces
User interfaces have the ability to change the way people

What Is Software Development?
In our modern world, it is difficult to imagine any

Why Is Software Development Important?
In our article, we will study the essence of software
Android application development is a step towards business development with the possibility of expanding the audience exponentially. This conclusion is due to the record number of Google Play Market users (more than 1.5 billion).
We can offer:
- development of applications for PCs under Windows and Linux (C / C ++, Visual Studio, QT);
- database design and optimization (MySQL, Postgres SQL);
- development of console applications for the server (C / C ++, Perl, Bash Shell);
- software for embedded systems (x86, Atmel AVR, ARM);
- development of layouts and functional prototypes of user interfaces;
- mathematical modeling of processes (MathCAD, MathLab);
- consulting in the field of software development and its implementation.

Software development is one of our main directions. We can develop effective applications for PCs and mobile devices, as well as server platforms and embedded devices. We have several successfully completed and implemented large projects that confirm our capabilities.

Development of software for Microsoft Windows, custom-made web applications allows you to get the right software product for your business with minimal investment and risks. 1We have extensive experience in creating automation systems in areas where most ready-made software solutions are powerless.
We’ve Helped The Following Brands






Need an agile and efficient Dedicated development team to bring your idea to life? Perfectial is a technical partner to many high-profile companies around the world, we build, enhance, and maintain truly innovative software platforms.











Red Dog Casino is one of the market leaders in mobile gambling with up to date and secure data encryption software. There is an extensive and varied gaming portfolio of 250+ games and 225% Welcome Bonus if you join it today. We at Red Dog take pride in offering our players only the highest quality Android app casino software that accepts a wide variety of payment methods, including Mastercard, Visa, Neosurf, and that matches the needs of every Android operating system user.
On your Mac, you can utilize a program like VPN Unlimited to encrypt and cloak your online activity while safeguarding your important data.

Experts ranked the best custom software development companies on iTRate.co. Find the right software developer by cost, expertise, location and verified client reviews.




